When you first set up your WordPress security website, it may be the furthest thing from your mind. Many beginners assume that the installation, whether you install WordPress manually or from your hosting cPanel system, is secure. Bad assumption.
It may seem like no one would want to get into your website, but you should never take this for ‘granted’. Even with a new site, it does not take ‘bots’ to find your site and start attempting to log in or post spam comments.
This post discusses the most common ways ‘bots’ and hackers will try to access your WordPress site, and then lists some of the best methods to stop them.
Most common WordPress security issues
- Login Attempts
Many bots are set up to try to gain access to your site through the ‘wp-admin’ login panel.
- Spam Comments
Your site will get spam comments. The more popular your site gets the more spam comments. Some spam comments look good, but you can normally tell spam comments from the quirky email address used, and the poor English in the comment. If it does not look legit, delete the comment.
- Old Versions of WordPress
WordPress code is open source, so anyone has access to it. Hackers are always looking for ways to exploit that code to access websites with older versions of WordPress.
- Plugins
One of the great things about WordPress is the huge variety of plugins. For the most part, WordPress plugins are secure. Every now and then, some have code that hackers can exploit. A great example of this is the recent issue with the “timthumb” plugin. When an issue does occur, word spreads fast, and there is normally a quick update to resolve the issue.
Quick and easy methods to keep your WordPress website secure
- Keep the WordPress version on your website up to date.
In a previous post, Manual vs. Automatic Installation, I talked about the pros and cons of installing WordPress using your host cPanel or installing it yourself manually. The big advantage of installing WordPress manually is having the ability to update WordPress as soon as they are available. Often, when you are relying on cPanel for installing and updates, the hosting company will not allow an update until they evaluate it, which can be a long, unnecessary delay.
- Move WordPress site from HTTP to HTTPS
SSL (Secure Sockets Layer) uses a combination of Public Key and Private key to establish an encrypted connection between a web server and a web browser via HTTPS to secure data transmission from identity theft.
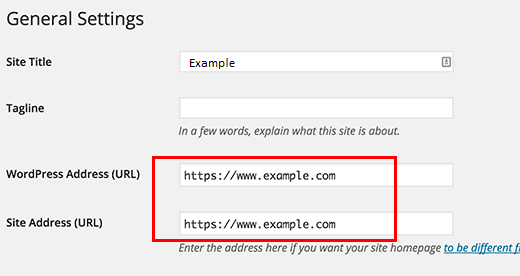
To move the WordPress site from HTTP to HTTPS, you need to get a basic type of inexpensive SSL certificate such as Comodo Positive SSL from an authorized provider. Then, You need to configure WordPress for SSL/HTTPS by updating code define(‘FORCE_SSL_ADMIN’, true); in your WordPress wp-config.php file. Ensure to update WordPress site URL address fields as seen below:
- Keep your plugins up to date.
- Delete unused plugins.
- Routinely back up your WordPress site.
This should be obvious. If something does happen to your website, it will be much easier to restore. I will post on how to backup your WordPress website soon.
- Use some form of “Captcha” plugin to help prevent spam.
WordPress comes with Askimet preinstalled. There are many other good captcha plugins available. User ratings and feedback can help you decide. Personally, I have found the “Captcha Free” plugin works well.
- Use the “Limit Login Attempts” plugin.
This is a great plugin for stopping the ‘brute-force’ login attacks on your website. If there are too many unsuccessful login attempts, then that IP address will be blocked from attempting to login.
This is a beginner’s guide, so there is much more to learn. I have included 2 links below to excellent articles on WordPress security that gives more detailed information and options.
If you have a favorite WordPress security plugin, please leave a comment and let us know.
Thanks for reading















